Build a Competitive Advantage With Professional Cybersecurity: A Board-Level Perspective + Reflection

In an era of relentless digital disruption, cybersecurity is no longer merely a “back-office” IT function or a box to be checked for compliance. It has evolved into a fundamental pillar of strategic differentiation. Organizations that want to build a competitive advantage with professional cybersecurity must shift their mindset from defence to value creation.
Companies that view cybersecurity through a purely defensive lens risk being left behind by competitors who leverage trust, resilience, and digital integrity as market-winning assets. This article explores why competitive advantage matters, how professional cybersecurity provides that advantage, and why a strategic partnership is the most efficient path to achieving it.
Key Takeaways
⦁ Trust is the New Currency: In a digital economy, trust is more valuable than physical assets. Professional cybersecurity is the tool to manufacture that trust.
⦁ Agility Requires Security: You cannot innovate at speed if you are constantly looking over your shoulder. Professional security provides the confidence to move fast and break ground, not things.
⦁ Partnership is Practicality: The complexity of modern threats makes a specialized partner more efficient and more effective than a purely internal model.
⦁ Board Governance is Value Creation: Moving security from an IT expense to a board-level strategy is the key to creating long-term shareholder value.
Why Build a Competitive Advantage?
Competitive advantage is the “moat” that protects a business’s profitability and market share. In a globalized, hyper-connected economy, traditional advantages like geographic location or physical scale are eroding. Digital transformation has leveled the playing field, making “agility” and “trust” the new frontiers of competition.
The Economic Imperative: Survival of the Fittest
Building a competitive edge is not just about growing faster than peers. It is about sustaining margins in a commoditized world.
A distinct advantage allows a firm to:
⦁ Command Premium Pricing: Customers are willing to pay more for reliability and data privacy. In many B2B sectors, a security audit is now a mandatory “pre-qualification” step. Companies with a superior security posture can skip these hurdles and win contracts faster.
⦁ Attract Top Talent: High-performing individuals want to work for industry leaders who prioritize integrity. A company that is perceived as “unstable” or “negligent” with its digital assets will struggle to recruit the very engineers and data scientists needed for growth.
⦁ Enhance Capital Access: Investors increasingly use Environmental, Social, and Governance (ESG) criteria, of which data security as a key component, to allocate capital. A “low-risk” profile from a cyber perspective directly translates to a lower cost of capital.
⦁ Expansion through M&A: During the acquisition process, the cyber hygiene of the target business is a critical factor in valuation. A company with a robust, professional security posture is a more attractive and more valuable acquisition target.
The Opportunity Cost of Stagnation
Without a clear competitive differentiator, a business becomes a price-taker, vulnerable to every market tremor. The “opportunity cost” of not building a competitive advantage is the lost revenue from customers who chose a more trusted competitor.
In the digital economy, this is not just a gradual decline but a rapid displacement.
Why Build a Competitive Advantage With Professional Cybersecurity?
The shift from “cybersecurity as a cost” to “cybersecurity as a revenue enabler” is the defining characteristic of modern high-performing boards.
1) Cybersecurity as a “Speed-Brake”: Accelerating Innovation
Consider a high-performance racing car. It doesn’t have world-class brakes, so it can stop; it has them, so it can go faster. Similarly, professional cybersecurity allows an organization to adopt emerging technologies like Generative AI and Cloud-native architectures with confidence.
When the foundation is secure, the business can innovate at a pace that competitors, hamstrung by legacy vulnerabilities, cannot match. For instance, a bank with a professional, agile security framework can launch a new mobile payment feature in weeks, while a competitor might take months just to clear the internal security hurdles. This “Time-to-Market” advantage is directly attributable to the professional security posture.
2) Trust as the Ultimate Differentiator: The “Digital Trust” Dividend
In a world of frequent data breaches, “Digital Trust” is a scarce and valuable commodity. According to McKinsey research, consumers are increasingly likely to switch brands after a security incident. A “Professional” cybersecurity posture, one that is proactive, transparent, and resilient, turns security into a brand promise.
It’s not just about keeping the hackers out; it’s about inviting the customers in. When a company can prove that it treats its customers’ data as its own most valuable asset, it builds a level of loyalty that marketing budgets alone cannot buy. This “Digital Trust Dividend” manifests in higher customer retention rates and a stronger, more resilient brand reputation.
3) Strategic Compliance: Moving Beyond the Floor
Regulatory frameworks like GDPR, HIPAA, and NIS2 set a “compliance floor.” However, true competitive advantage is found above that floor.
Professional cybersecurity uses compliance as a baseline but focuses on “Strategic Excellence.” This means anticipating future regulations and building systems that are “secure by design,” rather than “secure by reaction.”
The Model: The Board-Level Cyber-Advantage Framework
To transition to this new state, boards must adopt a holistic model that integrates security into the core business strategy.
The Three Pillars of Strategic Security:
⦁ Resilience: The ability to absorb shocks and maintain operations during an incident. This ensures that a cyber-event is a “minor disruption” rather than a “catastrophic failure.”
⦁ Digital Trust: Building a verifiable reputation for data stewardship and privacy. This becomes a key factor in B2B and B2C selection processes.
⦁ Operational Agility: Streamlined, secure workflows that allow for rapid product launches and pivot points without re-engineering the security stack.
Why Build a Competitive Advantage Together With a Professional Partner?
The “Do-It-Yourself” (DIY) era of cybersecurity is ending. The complexity of the threat landscape, combined with a global shortage of nearly 4 million cybersecurity professionals (World Economic Forum, 2024), makes in-house-only models increasingly risky and inefficient.
1) The Talent War: Accessing the “Elite 1%.”
A professional partner brings “Economies of Expertise.” They provide 24/7 Monitoring (SOC), Threat Intelligence, and Incident Response capabilities that most mid-to-large enterprises cannot build or maintain alone.
By partnering with a specialized firm, the board ensures the organization has access to the “Elite 1%” of cybersecurity talent experts who see threats across dozens of industries and can apply those insights to your business.
2) Efficiency Through Scale and Specialization: The ROI of Partnership
Developing an in-house security operations center (SOC) that is truly effective can cost millions of dollars in infrastructure and personnel. A professional partner allows the organization to “rent” this capability at a fraction of the cost, while gaining a much higher level of maturity.
This is not just “cost-cutting.” It is “capital allocation efficiency.” It frees up internal resources to focus on the company’s core mission.
3) Strategic Benchmarking and “Board-Ready” Insights
A professional partner doesn’t just manage the “how.” They help the board define the “what.” They provide the metrics, benchmarking, and reporting that allow board members to make informed decisions about resource allocation and risk appetite.
They can answer the question: “Are we spending too much, or not enough, compared to our peers?” with data-backed certainty. This level of strategic clarity enables a board to move from a “reactive” stance to a “proactive” value-creating leadership style.
4) Operational Agility: Scaling on Demand
In times of crisis or rapid growth (such as a merger or a global product launch), a professional partner can scale their security services instantly. An in-house team, by contrast, takes months to hire and train new staff.
This flexibility is a critical component of a “Competitive Advantage,” the ability to scale security at the same speed as the business.
Comparisons and Data
| Feature | Traditional (Compliance-Focused) | Modern (Competitive-Focused) |
|---|---|---|
| Board’s Role | Reviewing incident reports. | Steering security-driven growth. |
| Primary Goal | Meeting regulatory minimums. | Building market-leading trust. |
| Investment View | Necessary evil / Sunk cost. | Strategic investment / Value driver. |
| Response to AI | Hesitation and restriction. | Controlled, secure experimentation. |
| Customer Impact | Invisible until something breaks. | A visible pillar of the brand promise. |
Table 1: Compliance Focused vs. Competitive Focused Cybersecurity
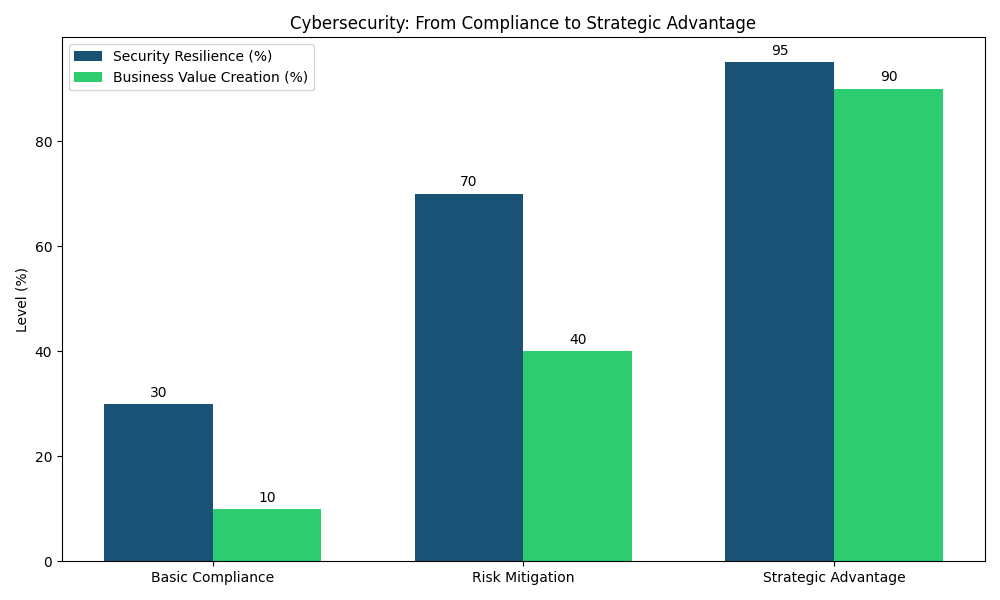
Chart: From Compliance to Strategic Advantage
The chart below illustrates the correlation between cybersecurity maturity and business value creation. While “Basic Compliance” provides minimal protection, “Strategic Advantage” security postures drive significant resilience and value.
Reflection: A Board-Level Checklist for the “Cyber-Advantage” Era
To conclude, we invite you to reflect on your current posture. A competitive advantage is not a destination but a continuous pursuit. Building it requires more than just capital. It requires a cultural shift in how the board and the executive team perceive security.
Critical Questions for the Board:
⦁ Is our CISO a “Risk Manager” or a “Business Leader”? Does their reporting focus on technical vulnerabilities or on how security enables new market opportunities? If the board meeting only discusses “what was blocked,” it is a missed opportunity to discuss “what can we build?”
⦁ How would our customers describe our data stewardship? Is it a reason they stay with us, or a risk they “tolerate”? A brand that is “trusted by default” is the most powerful marketing engine in the digital economy.
⦁ If a major incident occurred today, would we be “Resilient” or “Reactive”? Do we have a professional partner on retainer who knows our environment as well as we do? Resilience is built in the months before an incident occurs, not in the hours after.
⦁ Are we using cybersecurity as a “speed-brake” to innovate faster with AI and Cloud? Or are we falling behind because our security processes are too slow? Organizations that “fear” technology because of security risks are inherently at a disadvantage to those that “harness” it through professional security.
The Role of Leadership: Setting the Tone from the Top
The board’s most important contribution to cybersecurity is not technical oversight, but “Cultural Direction.” When the board asks about the “strategic value” of security, the rest of the organization follows. This is the difference between a company that “has” a security policy and a company that “is” a secure, trustworthy partner.
At Axelris, we believe that professional cybersecurity is the bedrock of future-ready organizations. By moving beyond the “defend-at-all-costs” mentality and embracing a “secure-to-win” strategy, boards can transform a traditional liability into their most powerful competitive advantage.
The choice is yours: will you be a “risk-taker,” or a “trust-maker”?
Conclusion
Cybersecurity is no longer a defensive necessity alone. It is a strategic engine for trust, resilience, and growth. Boards that treat security as a competitive asset can innovate faster, strengthen stakeholder confidence, and improve enterprise value.
With the right professional partner, cybersecurity becomes more than protection. It becomes a market advantage, helping organizations lead with confidence in an increasingly uncertain digital economy.
© 2026 Axelris Technologies International, Inc. All rights reserved

